What Is 567gk3 Identifier in Technology
When I first encountered a string like 567gk3 inside a development log, it looked meaningless, like static noise in a technical report. But inside modern computing systems, these small clusters of characters carry enormous responsibility. A code like this typically represents a short alphanumeric identifier, a compact label used by digital systems to uniquely identify something such as a device, session, process, or software version.
In practical terms, identifiers like 567gk3 exist so computers can tell one thing apart from another. A server handling thousands of simultaneous requests must know which user session belongs to which browser. A software team managing hundreds of updates must know which build is being tested. These identifiers solve that problem quickly and reliably.
The importance of such identifiers has grown dramatically with the expansion of cloud computing, global networks, and billions of connected devices. Modern systems rely on compact identifiers because they are efficient, easy to store, and capable of generating billions of unique combinations.
What appears to be random is usually the result of deliberate engineering. Developers generate identifiers through algorithms designed to minimize duplication, improve traceability, and increase security. Whether embedded in a database entry, a cloud resource label, or a software log file, these short codes serve as a fundamental organizing principle of digital infrastructure.
Understanding identifiers like 567gk3 reveals an essential truth about modern technology. Beneath the sleek interfaces and powerful applications lies a quiet framework of labels and references that allows vast digital systems to function smoothly.
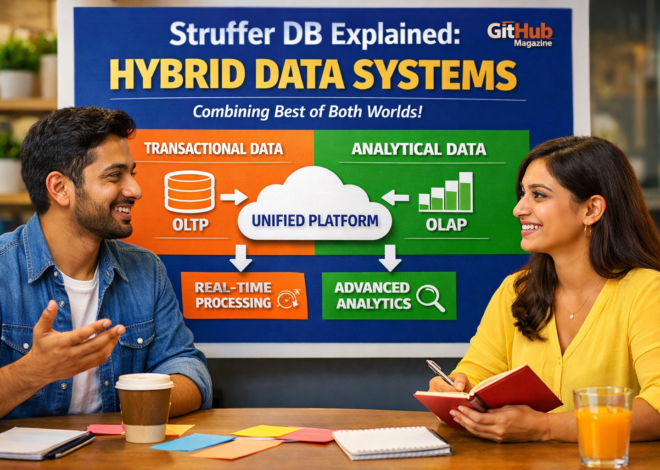
The Quiet Infrastructure of Digital Identity
Short alphanumeric identifiers emerged as computing systems expanded beyond individual machines into distributed networks. Early software environments often relied on simple sequential numbers or file names to label resources. That approach worked when systems were small, but it became unreliable as applications scaled across servers, organizations, and global infrastructure.
Engineers began using combinations of letters and numbers to create compact identifiers capable of representing enormous numbers of unique elements. A code such as 567gk3 might represent a temporary session, a device within a network, a record in a database, or a reference inside a development environment.
These identifiers serve as digital name tags. Whenever a system component communicates with another component, the identifier helps clarify exactly which resource is being referenced. This prevents confusion when multiple processes are running simultaneously.
Without identifiers, even basic operations such as debugging software or analyzing system performance would become extremely difficult. Developers depend on identifiers when tracing errors, identifying user activity, or locating the precise version of software running within a system.
In large organizations managing thousands of servers and services, identifiers allow engineers to coordinate complex operations. They make it possible to reference a precise component without ambiguity.
The simplicity of a short string like 567gk3 hides the scale of the digital ecosystems it helps organize.
Why Short Identifiers Matter in Modern Systems
Modern computing environments operate at extraordinary scale. Cloud services handle millions of transactions every second. Online platforms support billions of user interactions daily. Each interaction requires reliable tracking and identification.
Short identifiers perform three essential functions: organization, traceability, and security. They allow systems to maintain order while managing huge volumes of data and processes.
One major benefit is traceability. If a system fails or produces unexpected behavior, developers can examine logs that contain identifiers tied to specific operations. By following those identifiers, engineers can reconstruct what happened and identify the root cause of the problem.
Another advantage is efficiency. Compact identifiers reduce storage overhead and transmission size when data moves across networks. In high-performance environments, even small reductions in data size can improve system responsiveness.
The following table highlights common roles played by short identifiers.
Common Roles of Short Identifiers in Technology
| Function | Description | Example Application |
|---|---|---|
| Session tracking | Identifies a user session during login activity | Web authentication systems |
| Device identification | Distinguishes individual devices in a network | IoT devices and sensors |
| Version control | Labels specific software builds | Software development pipelines |
| Resource tagging | Assigns labels to system resources | Cloud computing platforms |
Because these identifiers enable reliable referencing, they form an invisible layer of infrastructure that supports the modern internet.
Anatomy of a Six-Character Identifier
A six-character identifier such as 567gk3 is intentionally compact but capable of representing an enormous number of combinations. The design typically blends digits and letters to maximize variability while keeping the code short.
Each additional character dramatically increases the number of possible combinations. This property allows short identifiers to scale effectively.
Approximate Identifier Combination Capacity
| Identifier Length | Possible Combinations |
|---|---|
| 4 characters | About 1.6 million |
| 6 characters | Over 56 billion |
| 8 characters | Trillions of combinations |
Even a modest six-character identifier can represent tens of billions of unique values. For many applications, that range is more than sufficient.
Identifiers are usually generated by algorithms rather than humans. These algorithms may rely on random number generation, hashing techniques, or timestamp-based calculations. The goal is to create identifiers that are unique and difficult to predict.
Predictability can introduce security vulnerabilities. If an attacker can guess the next identifier in a sequence, they might gain unauthorized access to another user’s session or data. For this reason, many systems rely on cryptographically secure random generators to produce identifiers.
This careful design ensures that short identifiers remain both practical and secure.
From Software Builds to Smart Devices
Short identifiers appear across nearly every corner of modern technology. Software development teams use them to label specific builds and revisions of code. When testing new features, developers reference these identifiers to track which version of the software produced a particular result.
Hardware manufacturing also relies on identifiers. Electronic components and devices often carry short codes that indicate manufacturing batches, firmware revisions, or internal tracking numbers. These codes help companies manage quality control and product support.
Cloud computing environments depend heavily on identifiers as well. Virtual machines, containers, APIs, and storage resources are all labeled with identifiers that allow platforms to manage them efficiently. Without these labels, coordinating large-scale infrastructure would be nearly impossible.
In research and development environments, identifiers often represent experimental builds or prototypes before official product names exist. Engineers can reference a short identifier to discuss a configuration without confusion.
Across these environments, identifiers provide clarity. They allow complex systems to operate with precision even when thousands of components interact simultaneously.
Security and the Evolution of Digital Tokens
Security systems frequently rely on identifiers to maintain authenticated connections. When a user logs into a website, the server generates a session token that represents that user’s authenticated session.
Every request sent to the server includes this token. The server checks the token to verify that the request originates from a valid session. Without such identifiers, users would need to re-enter credentials for every action.
Session identifiers must be generated carefully to prevent misuse. If the token is predictable, attackers may attempt to guess it and impersonate legitimate users.
Modern authentication systems therefore rely on random or cryptographic token generation methods. These methods produce identifiers with sufficient randomness, often referred to as entropy, making them extremely difficult to predict.
Security engineers also implement practices such as token expiration and rotation. These measures limit the lifetime of an identifier so that even if it were compromised, the window of vulnerability would remain small.
Short identifiers, when properly generated and managed, can therefore serve as both organizational tools and security mechanisms.
The Expanding Role of Identifiers in the Internet of Things
The rapid expansion of the Internet of Things has increased the importance of reliable identifiers. Billions of connected devices now communicate with cloud platforms, industrial systems, and data networks.
Each device requires a unique identity so that platforms can track its behavior and manage its configuration. Identifiers allow systems to monitor device activity, update firmware remotely, and apply security permissions.
In industrial environments such as warehouses or manufacturing facilities, identifiers attached to sensors and equipment enable real-time monitoring. Managers can track asset movement, equipment performance, and operational efficiency through digital dashboards.
Smart cities also rely on device identifiers to coordinate traffic systems, energy grids, and public infrastructure sensors. These identifiers allow data collected from thousands of devices to be organized and analyzed effectively.
Without identifiers, managing billions of connected devices would be nearly impossible. The growth of IoT technology therefore continues to reinforce the importance of digital identification systems.
The Hidden Challenge of Identifier Management
Although identifiers are essential, they introduce technical challenges that developers must carefully manage. One common issue is identifier collision, which occurs when two elements accidentally receive the same identifier.
While rare in well-designed systems, collisions can create confusion or cause operations to reference the wrong resource. Engineers minimize this risk by designing identifiers with sufficient length and randomness.
Another challenge involves documentation. Systems often generate thousands of identifiers during development and operation. Without proper records, it can become difficult for engineers to determine what a specific identifier represents.
Development teams address this issue by maintaining logs, timestamps, and metadata associated with identifiers. These records allow engineers to trace identifiers back to their original context.
Proper management practices ensure that identifiers remain reliable tools rather than sources of system complexity.
Why Developers Often Prefer Short Identifiers
Long identifiers such as globally unique identifiers provide extremely large uniqueness ranges, but they are often cumbersome to read and manage. Developers frequently prefer shorter identifiers because they are easier to interpret when scanning logs or debugging software.
Short identifiers also work well in URLs, configuration files, and system dashboards where space is limited. Their compact form reduces visual clutter while still providing sufficient uniqueness for most applications.
The balance between usability and uniqueness explains why many modern platforms adopt shorter identifier formats. When generated properly, these identifiers remain reliable while improving developer productivity.
This balance reflects a broader design philosophy in engineering. Systems should remain powerful yet practical. Short identifiers represent a solution that satisfies both requirements.
Key Takeaways
- Short alphanumeric identifiers such as 567gk3 help digital systems uniquely label components, sessions, and resources
- These identifiers enable organization, debugging, and secure communication within complex technological environments
- Even small identifiers can represent billions of combinations when letters and numbers are combined
- Developers rely on identifiers across software development, cloud computing, and hardware manufacturing
- Security systems use identifiers as authentication tokens to maintain trusted user sessions
- The rapid expansion of connected devices has increased the importance of reliable identification systems
- Effective identifier management requires randomness, documentation, and monitoring
Conclusion
A string like 567gk3 might appear insignificant at first glance, but it represents a fundamental building block of modern computing. In vast digital systems where millions of components interact simultaneously, identifiers provide the structure that keeps everything organized.
They allow servers to recognize sessions, developers to trace software behavior, and networks to distinguish between devices. Without these identifiers, managing the scale and complexity of contemporary technology would be far more difficult.
The continued expansion of cloud platforms, artificial intelligence systems, and connected devices ensures that identifiers will remain central to digital infrastructure. Engineers will continue refining how these identifiers are generated, secured, and managed in order to support even larger systems.
Ultimately, identifiers embody a simple but powerful principle: complex systems function best when every element can be uniquely identified. Behind every short code lies an entire ecosystem of technology working together to keep the digital world running smoothly.
FAQs
What is an identifier like 567gk3 used for
It is typically used as a short alphanumeric label within digital systems to uniquely identify sessions, devices, software builds, or database records.
Are identifiers like this random
They are usually generated by algorithms designed to produce unique or unpredictable combinations rather than being manually created.
Can these identifiers be used for security
Yes, many authentication systems use identifiers as session tokens or temporary access keys that verify a user’s identity.
Why not use long identifiers everywhere
Long identifiers offer extreme uniqueness but are harder to read, store, and manage. Short identifiers often provide a better balance of usability and scalability.
Where might someone see identifiers like this
They appear in software logs, cloud resource labels, database entries, authentication systems, and connected device networks.